Log Management, delivered as a service…
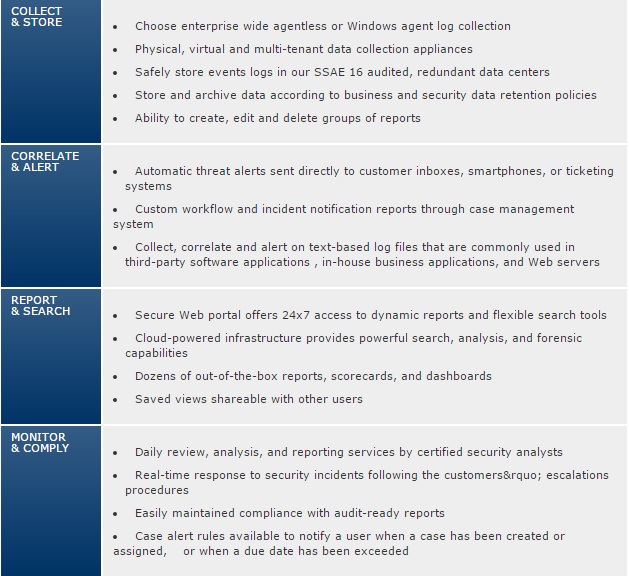
SALIX’s unique Security-as-a-Service model offers you a cost-effective and easily managed way to reap the benefits of log management:
- Maintain compliance with reliable log collection and daily log reviews
- Improve security by leveraging log data to mitigate intrusion and security breaches
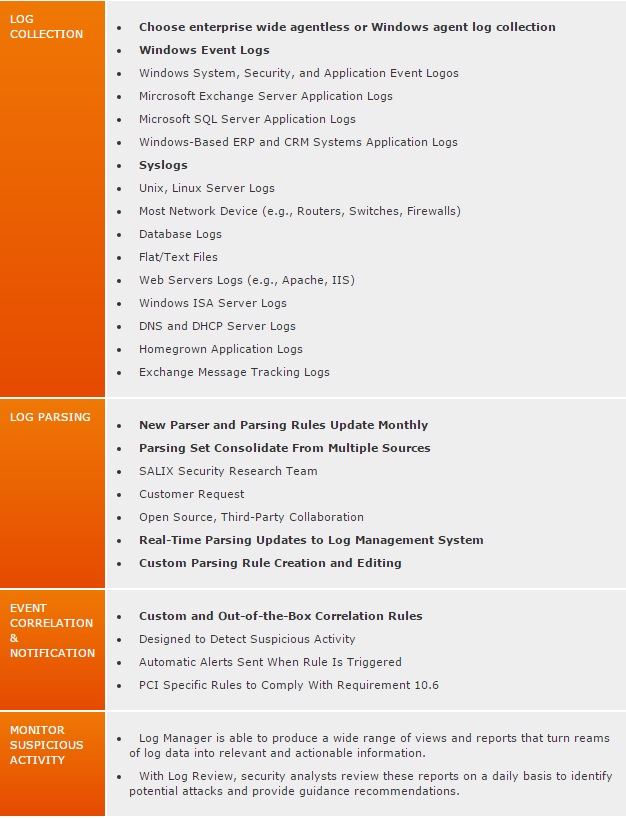
Log Manager collects, aggregates and normalizes log data, wherever it resides. Flexible data collection options – physical or virtual sensors with agent-based or agentless methodology – ensure minimal impact on your infrastructure. Once logs are transferred securely to SALIX, data is parsed and normalized for real-time analysis or scheduled reporting. Log data is stored and securely to protect against unauthorized loss, access or modification.
Log Review is a service enhancement to Log Manager and provides daily event log monitoring by SALIX’ dedicated team of security professionals. With Log Review, log analysis is never delayed or sidetracked by competing priorities.
Log Manager and Log Review also include integrated review and case management capabilities. Track and report on incident trends across your entire enterprise, including services hosted outside of your perimeter. Built-in workflow and case management tools provide an auditable trail of any suspicious findings and give a historical perspective of your entire security and compliance operation.